Log4j Vulnerability in Calculator Providers
CUSTOMERfirst® Avoids Log4j, Others are Not So Fortunate
The Log4j vulnerability has been headline news across the Internet, a veritable 5-alarm fire for security professionals. Discovered late last month by a security researcher at Alibaba Cloud and reported to the Apache Software Foundation, companies are scrambling to understand their exposure and install fixes.
The flaw in Log4j creates a remote code execution vulnerability. This type of vulnerability allows an unauthenticated remote actor to seize control of your system(s), steal data, install ransomware, and engage in other harmful and malicious acts. The combination of the ubiquity of Log4j and the control afforded to a remote actor by this exploit makes this one of the most serious, internet-wide security holes in recollection.
When data on this vulnerability was first made available by U.S. cyber security authorities, Leadfusion immediately commenced a full stack analysis of its CUSTOMERfirst platform, including all hardware and software components. Leadfusion’s security team has determined that no element of its CUSTOMERfirst platform stack is subject to this exploit.
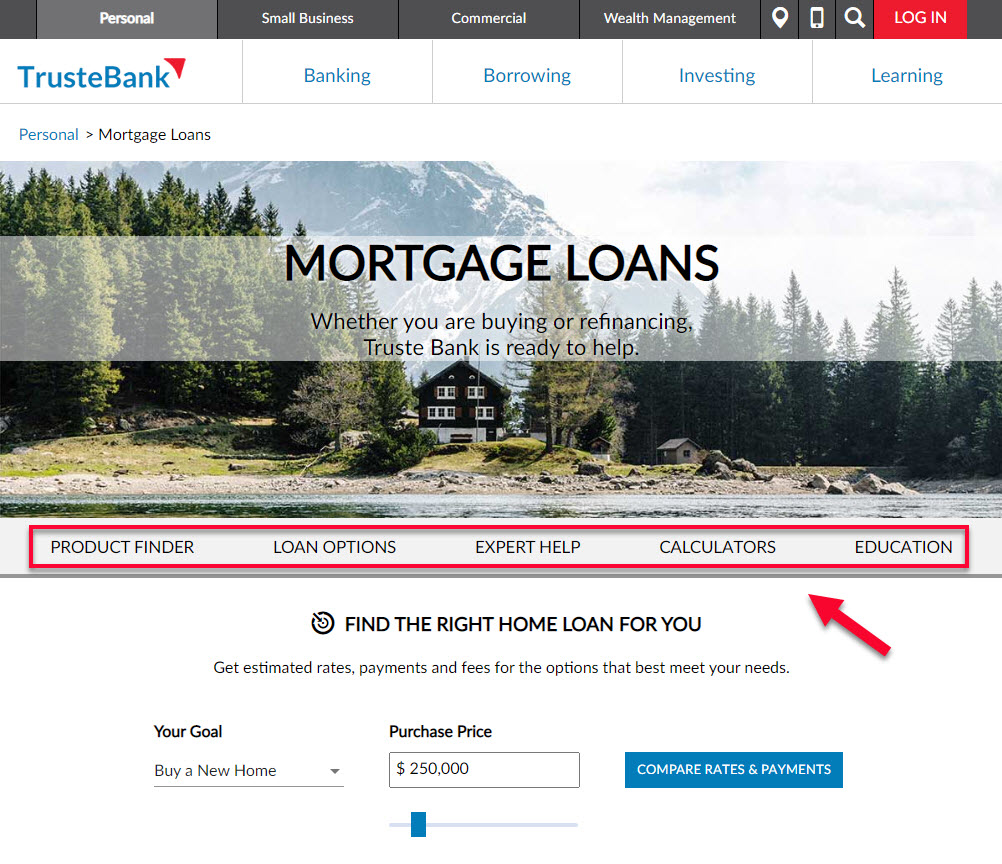
Our research shows that there are a multitude of other tools on the market that are subject to this exploit. We encourage all banks, credit unions, and other financial service providers to carefully review their risk in the context of Log4j.